One Time Pad encryption, also known as the Vernam or perfect cipher, is the holy grail of encryption security, when used correctly it makes cryptanalysis nearly impossible because it is not possible to compare old messages. As long as the one time pad is perfectly random all the clues on what coding was used for encryption remain in a single message, it is not easy to accomplish because high quality random numbers are difficult to generate.
This type of encryption was widely used by spy agencies during World War II and the Cold War period, protecting diplomatic and military communications, the advantadge of one time pad encryption is that it can done by hand with pencil and paper, without the need to carry any special device compromising undercover operations. A downside for this type of encryption is that the password is made up of as many characters as the text you encrypt, resulting in extremely long passphrases difficult to disseminate. When all rules are followed this one time encryption method remains secure and unbreakable but in order to solve the key transmission problem one time pads have been replaced by symmetric block ciphers and public key encryption.
I have only managed to find old one time pad encryption tools, most of them developed by a single hobbyist and could be listed as abandonware, you should not assume developer’s claims are truth just because he says so, without truly random numbers one time pad security will be compromised and reusing any part of the pad makes the cipher vulnerable to attack, there is no way to know for sure how secure these programs are but some of them provide the source code for you to look at it.
CT-46 One Time Pad: An encryption tool that converts text into digits using a conversion table and completing the final group with zeros, the software is meant to be used to learn working with one-time pads and as a training resource, it comes with a complete help manual that tells you how to perform one time pad encryption with pencil and paper.
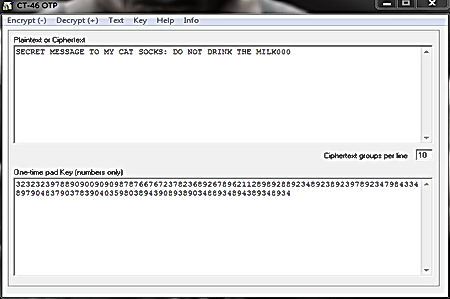
CT-46 One Time Pad encryption
OneTimePadJava: Written entirely in Java, it comes with the source code but no help manual although it appears to be easy to operate, the tool doesn’t need installation and works across platforms.
Pidgin Paranoia: A Linux plug in for the Pidgin messenger, providing secure IM conversations using one time pad encryption, the secret message has the same length as the key and it is only used once.
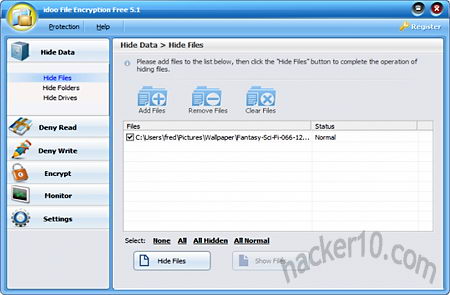
Solid Encryption($$): A commercial program claiming to be able to perform one time pad encryption, you can try it free for 30 days before being required to buy it. I found the interface to be outdated and not very easy to work with but it comes with a help page.

One Time Pad Solid Encryption
Cryptomni: A program to encrypt files using the one time pad cipher, a key file is created using the random generator SecureRandom, the source code is open, this program has not been updated for many years.

Cryptomni One Time Pad
OneTimePad Net: A one time pad encryption implementation using Visual Basic, an object-oriented computer programming language that needs Microsoft .NET to work, I had to right click and run this program as administrator for it to work, there is no help file but the interface is pretty straight forward.
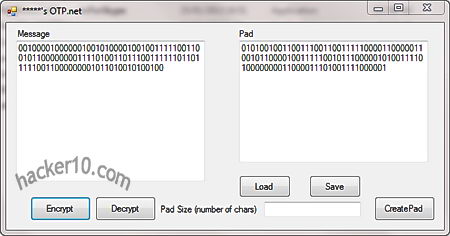
One Time Pad .NET encryption
Perfenc: A Unix program to perform one time pad encryption, documentation is included with the software typing man perfenc, you can install it from source with the usual build tools like cmake.
Emus encryption tool: It uses polyalphabetic methods from the middle ages, texts are encrypted with random codes and fixed passwords but can also be used as one time pad with extreme long random passwords and codes.

Emus encryption One Time Pad
Fxor: A Unix command line open source tool released under the BSD license that can be used for key file or one time pad encryption. This program is for people comfortable using the command line as you will have to compile it before being able to use the program. A help file is included.

Ron de Jong
FinalCrypt is an opensource easy multi-platform and powerful tool capable of mass encrypting files and directories from either a GUI or fully functional command line interface combining security, speed & simplicity.
Ron de Jong
Looking at the one time pad encryption tools above, you’ve got to see FinalCrypt:
http://www.finalcrypt.org/
Marco Gutenberg
Finalcrypt should be on the top of this list, it’s the only one time pad encryption that got internal approval to be used in the swiss exchange.
Wandee Thaweetham
After Crypto AG anything getting approved in Switzerland is suspicious.